Enhancing Web Application Security in Vehiculos-SENACAB
Introduction
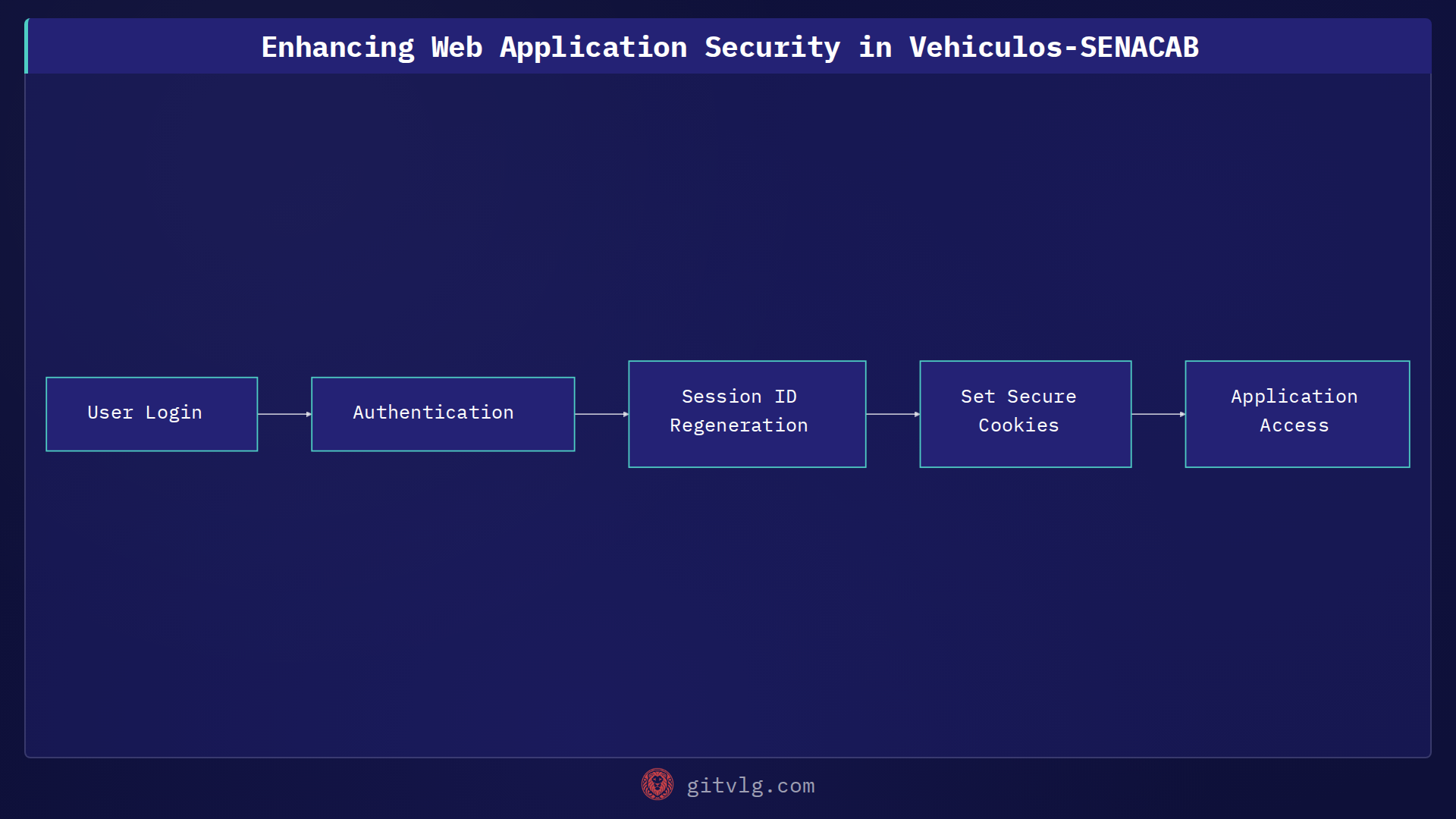
Securing web applications is a continuous process. Recent work on the Vehiculos-SENACAB project focuses on addressing several critical security vulnerabilities to protect user data and prevent potential attacks.
Key Security Enhancements
This iteration includes several vital updates to bolster the application's security posture:
-
CSRF Token Implementation: Cross-Site Request Forgery (CSRF) attacks are mitigated by implementing CSRF tokens across 14 forms within the application, including those utilizing Bootstrap. This ensures that requests originate from legitimate users and not malicious sites.
-
Session ID Regeneration: Upon successful login, the session ID is now regenerated. This prevents session fixation attacks, where an attacker might try to hijack a user's session by predetermining the session ID.
-
Secure Cookies: Cookies are now configured with the
Secureflag, ensuring they are only transmitted over HTTPS. This protects the cookie data from being intercepted over insecure connections. -
Disabling Debug Mode: The
APP_DEBUGsetting is set tofalsein the production environment (src/module/component.file). This prevents sensitive debugging information from being exposed to end-users, reducing the risk of information leakage. -
Upload Sanitization: Input sanitization has been implemented in the vehicle form editing feature. This prevents malicious code from being injected through uploaded files.
-
Random Data Generation: To enhance security,
bin2hex(random_bytes)is used insolicitar.phpfor generating random, cryptographically secure strings. -
Rate Limiting: Rate limiting is implemented in
login.phpandbootstrap.phpto prevent brute-force attacks by restricting the number of login attempts within a given timeframe. -
.env.example: An example environment file is provided as a template
Code Example: Session ID Regeneration
Here's an example of how session ID regeneration can be implemented in PHP:
<?php
session_start();
// Regenerate session ID to prevent session fixation
session_regenerate_id(true);
// Store user information in the session
$_SESSION['user_id'] = $user_id;
$_SESSION['username'] = $username;
?>
Conclusion
By implementing these security measures, the Vehiculos-SENACAB project significantly reduces its attack surface and protects sensitive user data. These changes showcase a commitment to secure coding practices and proactive vulnerability management. As a next step, consider implementing Content Security Policy (CSP) headers to further mitigate cross-site scripting (XSS) attacks.
Generated with Gitvlg.com